Blog
9 red flags to help you spot an email scam
December 7th, 2016

Every day hundreds of thousands of scam emails flow into the inboxes of users all across the world. While it’s painfully obvious that some are completely fraudulent, phishing emails – particularly those targeted at businesses – are becoming much more sophisticated, and increasing numbers of users are being tricked into sharing valuable company information.
Unfortunately, there is no one red flag which immediately identifies a scam email, but there are a number of things to watch out for.
How to spot a scam email
1. Don’t trust the displayed name in the email
A name displayed in the “from” box in Outlook is not a guarantee of the sender
2. Look but don’t click
If you hover your mouse over a link (without clicking) you will see the web address that the link points. If it doesn’t directly reflect that of the sender then be cautious. Also be extra vigilant if any email directs you to a website asking for a login, as this is the main way a criminal will steal valid login credentials.
3. Check for spelling or grammar mistakes
If the email doesn’t sound right when reading it then that’s a flag that it’s not legitimate
4. Look at the salutation
If your contact usually addresses you by your first name, but now they’re writing “Valued Customer”, you should look deeper. Again, any suspicion you have is probably being triggered correctly – trust your instincts.
5. Never give sensitive information
If an email is asking for sensitive information over email or a web page that you wouldn’t be comfortable with anyone else seeing then pick up the phone to a known number and validate it.
6. Beware of “urgency”
If an email sounds urgent and startling then do take some time to think, analyse or ask advice. If someone is threatening to stop a service or is making a demand then you should stop, think about it, and talk to your colleagues.
7. The images and layout in an email tell the truth
It’s common for cyber-criminals to not quite get the look of emails right, in terms of images and layout. You alarm bells should ring if the email doesn’t look quite right. If in doubt, pick up the phone.
8. Check the domain
Many spoof emails use a domain that is close to the legitimate domain. For example, someone could use paypall.com rather than paypal.com to fool a recipient.
9. Be wary of attachments
Attachments in emails can be dangerous if the file type isn’t a standard application file, such as a .doc (word file), xls. (Excel file) or pdf. (PDF file). Be especially wary if the attachment is one of the following file types – “exe”, “bat”, “com”, “cmd”, “cpl”, “js”, “jse”, “msi”, “msp”, “mst”, “paf”, “wsh”, “wsf”, “vbs”, “vbe”, “psc1”, “scr”, “lnk”. Also be extra careful with zip files as they can often hide dangerous files from inferior email scanners and firewalls.
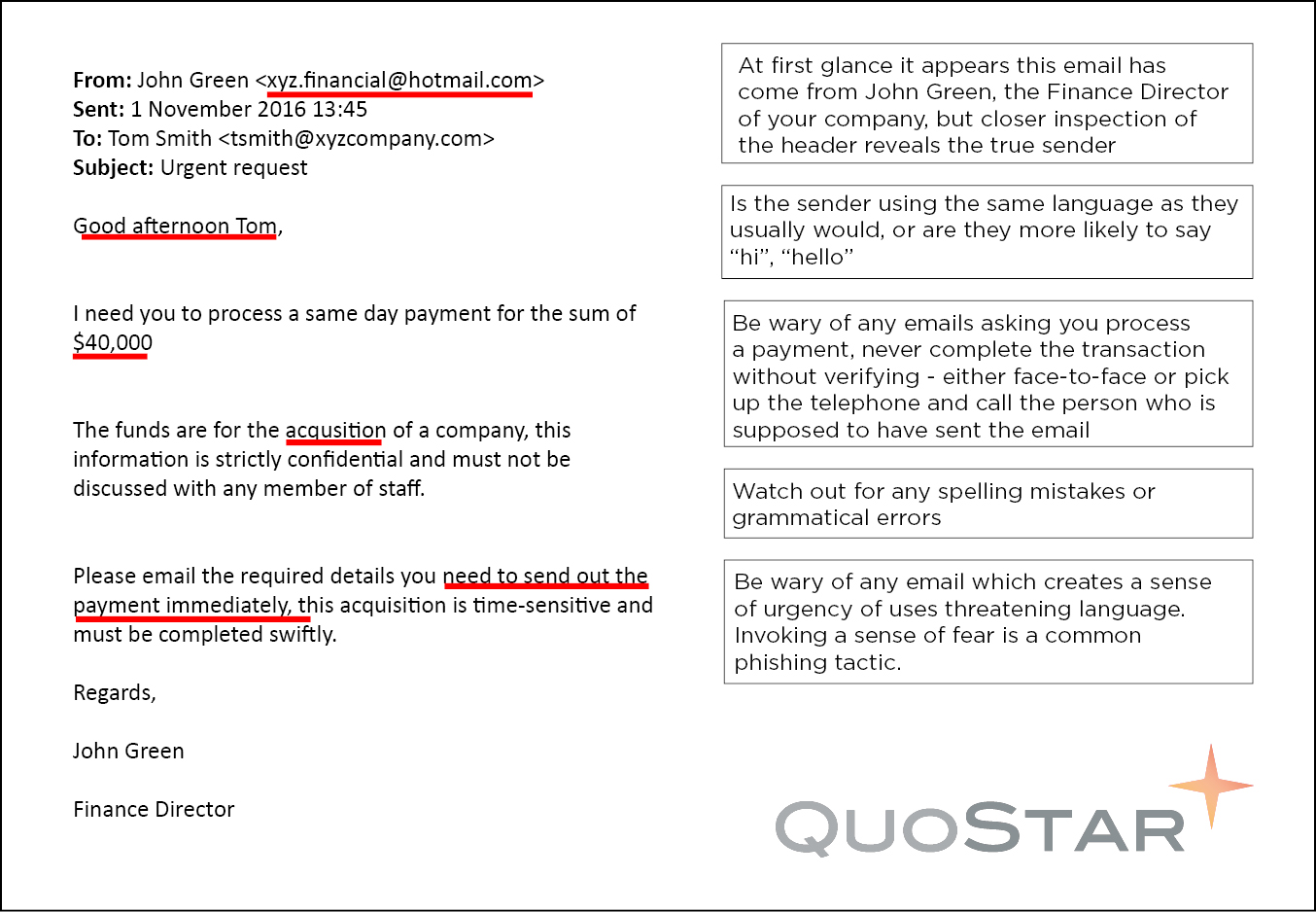
Example of a scam email
At the end of the day, if an email doesn’t seem quite right then make sure to qualify with the supposed original sender. If your Finance Director asks you to arrange a bank transfer, confirm the request on the phone or in person. It only takes a few minutes and could prevent you from making a costly mistake.
NEXT>> How to identify 4 common types of scam emails
How does the cloud and SaaS affect business continuity planning?
I regularly receive questions in relation to cloud and Software as a Service (SaaS), and how it affects Business Continuity plans. So I have compiled these into a blog article. The areas covered are a good starting point if you’re looking into your disaster recovery/business continuity plans in relation to cloud or SaaS. How can […]
Which type of IT support is best for my business?
One of the easiest ways for companies to gain other business efficiencies is to outsource part, or all, of their IT to a managed services provider. There are many options available and in today’s blog, we will discuss what each one will typically include. While the exact names may vary dependent on the provider, the following […]
The Cloud Migration Guide – Part 4: How to achieve a successful cloud migration
Welcome to the final instalment of the Cloud Migration Guide. If you’ve missed an earlier part or would like a recap, click here to view: Part 1: What is a cloud migration | Part 2: The risks and rewards of migration | Part 3: Factors which influence cloud readiness. Cloud migration has a lot to […]